Weekly Cyber Intel Brief - Week of March 9-13, 2026
Iran-linked hackers mass-wiped Stryker devices via Microsoft Intune, a year-long TriZetto healthcare breach exposed 3.4 million patients, and ShinyHunters harvested data from 100 Salesforce Experience Cloud customers.
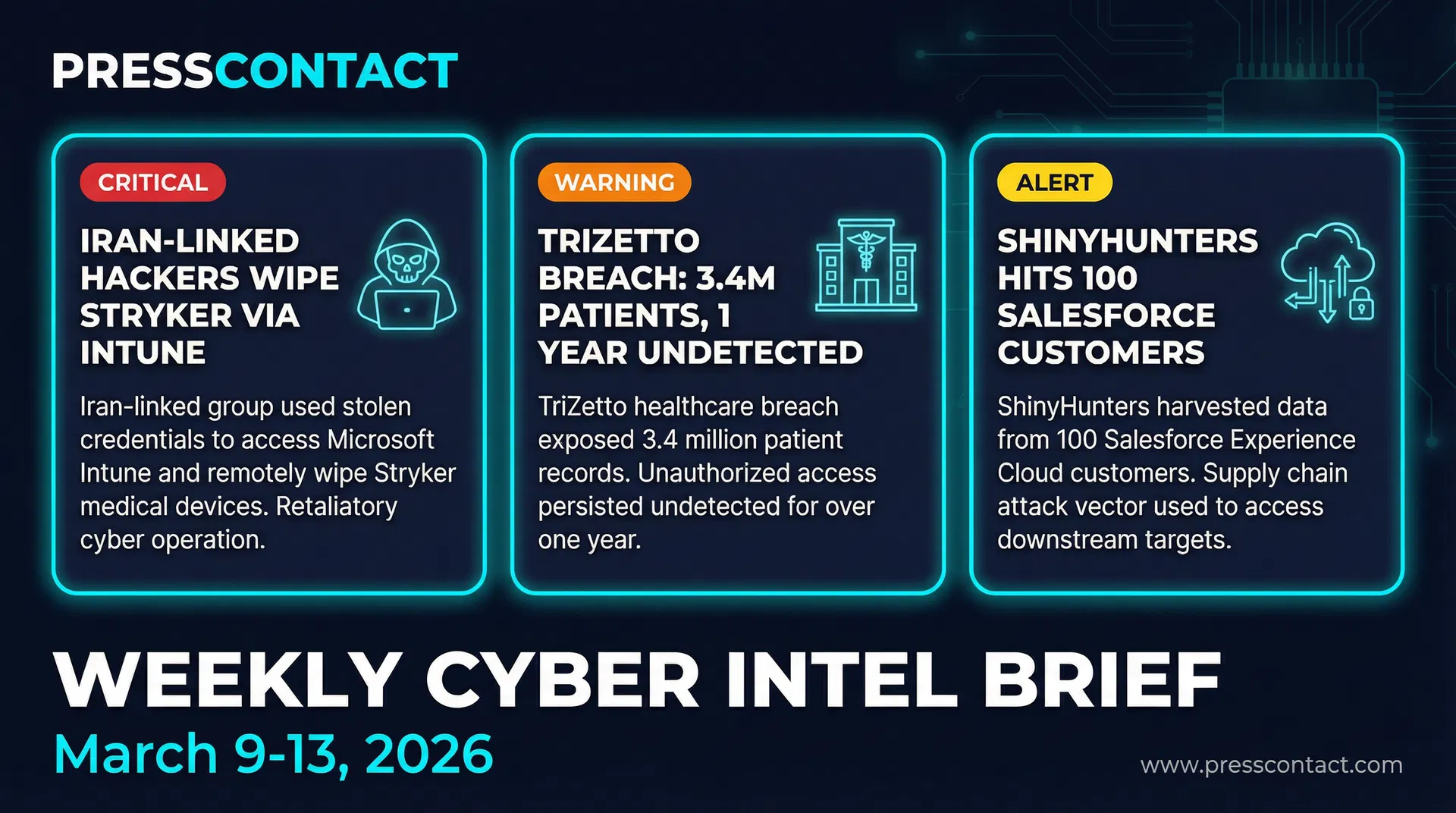
PressContact tracks the cybersecurity stories generating the most media coverage and security team attention each week. Here are the three that defined the week of March 9-13, 2026.
1. Iran-Linked Hackers Mass-Wipe Stryker Devices via Microsoft Intune
An Iran-linked hacking group claimed responsibility for a major cyberattack against Stryker (NYSE: SYK), one of the world's largest medical device companies, headquartered in Portage, Michigan. The attack reportedly disabled approximately 200,000 devices and extracted an estimated 50TB of data. Employees reported that work-issued phones and laptops stopped functioning entirely on the morning of Wednesday, March 11, 2026.
The attackers obtained employee login credentials and gained access to Stryker's Microsoft Intune account - the corporate mobile device management (MDM) platform. They then used Intune's legitimate remote wipe feature to mass-erase devices across the organization. Rather than deploying custom malware, the threat actors weaponized a standard IT management tool. Kevin Mandia, CEO of Armadin, described it as a "clever" and unexpected method that can bring a company to a halt without triggering traditional malware detection.
Attribution is consistent with Iran's documented pattern of retaliatory cyber operations following U.S.-Israeli military strikes. Check Point Research mapped multiple Iran-linked clusters - including Cotton Sandstorm, Educated Manticore, MuddyWater, Handala, and Agrius - conducting espionage, disruption, and influence operations in the current conflict period.
2. TriZetto Healthcare Breach - 3.4 Million Patients, One Year of Undetected Access
TriZetto Provider Solutions (TPS), a healthcare technology company owned by Cognizant, disclosed a data breach affecting 3,433,965 individuals. The company filed a breach notification with the Maine Attorney General and began notifying affected patients this week.
An unauthorized threat actor first gained access to a web portal used by TriZetto's healthcare provider customers in November 2024. The intrusion went undetected until October 2, 2025 - nearly a year of active data exfiltration. Notifications to affected individuals were issued in early March 2026, following the completion of the forensic investigation. The breach included names, birth dates, Social Security numbers, health insurance member numbers, provider names, and other demographic and health data. TriZetto supports approximately 200 million members and 875,000 healthcare providers.
3. ShinyHunters Harvests Data from 100 Salesforce Experience Cloud Customers
The ShinyHunters cybercrime group claimed responsibility for a data theft campaign targeting Salesforce Experience Cloud customers. The group states it has stolen data from approximately 100 high-profile companies by exploiting misconfigured guest user permissions in Salesforce's public-facing Experience Cloud sites.
Attackers used a modified version of AuraInspector - an open-source tool originally developed by Mandiant to help defenders audit Salesforce Aura framework configurations. ShinyHunters weaponized it to mass-scan public-facing Experience Cloud sites, probe the /s/sfsites/aura API endpoint, and query Salesforce CRM objects without authentication where guest user profiles had excessive permissions. The group claims it began exploiting insecure configurations in September 2025 and started using the modified tool in January 2026.
Salesforce confirmed the attack campaign on March 7, 2026, noting it does not involve a platform vulnerability but rather customer misconfiguration. The company urged customers to enforce a "Least Privilege" access model, disable unauthenticated API access, and restrict guest user permissions.
Also on the Radar
- AkzoNobel:Anubis ransomware group claimed 170 GB stolen, including employee and financial records, from the global paint manufacturer's U.S. site. (Check Point Research, March 9)
- LexisNexis:Attackers claimed theft of 3.9 million records, including approximately 400,000 user profiles and some government accounts. Company says exposed systems held mainly pre-2020 legacy data. (Check Point Research, March 9)
- Chrome/Edge AI Extensions:Researchers uncovered AI-themed browser extensions harvesting LLM chat histories and browsing activity from 900,000 users across 20,000 enterprise environments. (Check Point Research, March 9)
- CVE-2026-0628 (Chrome/Gemini):Google patched a high-severity flaw in Chrome's Gemini AI panel allowing malicious extensions to inject code and access cameras and microphones. (Check Point Research, March 9)
PressContact publishes the Weekly Cyber Intel Brief to help security vendors, PR teams, and communications professionals stay current on the stories generating the most coverage and industry attention. If you work in cybersecurity PR and want to discuss any of these stories, reach out directly.