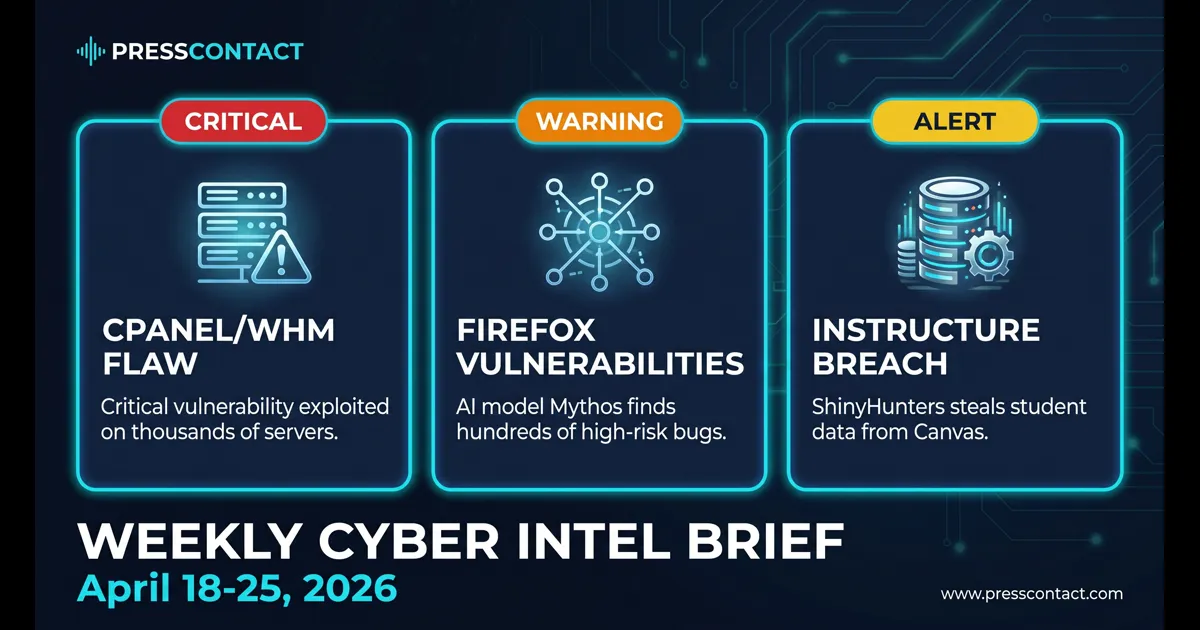
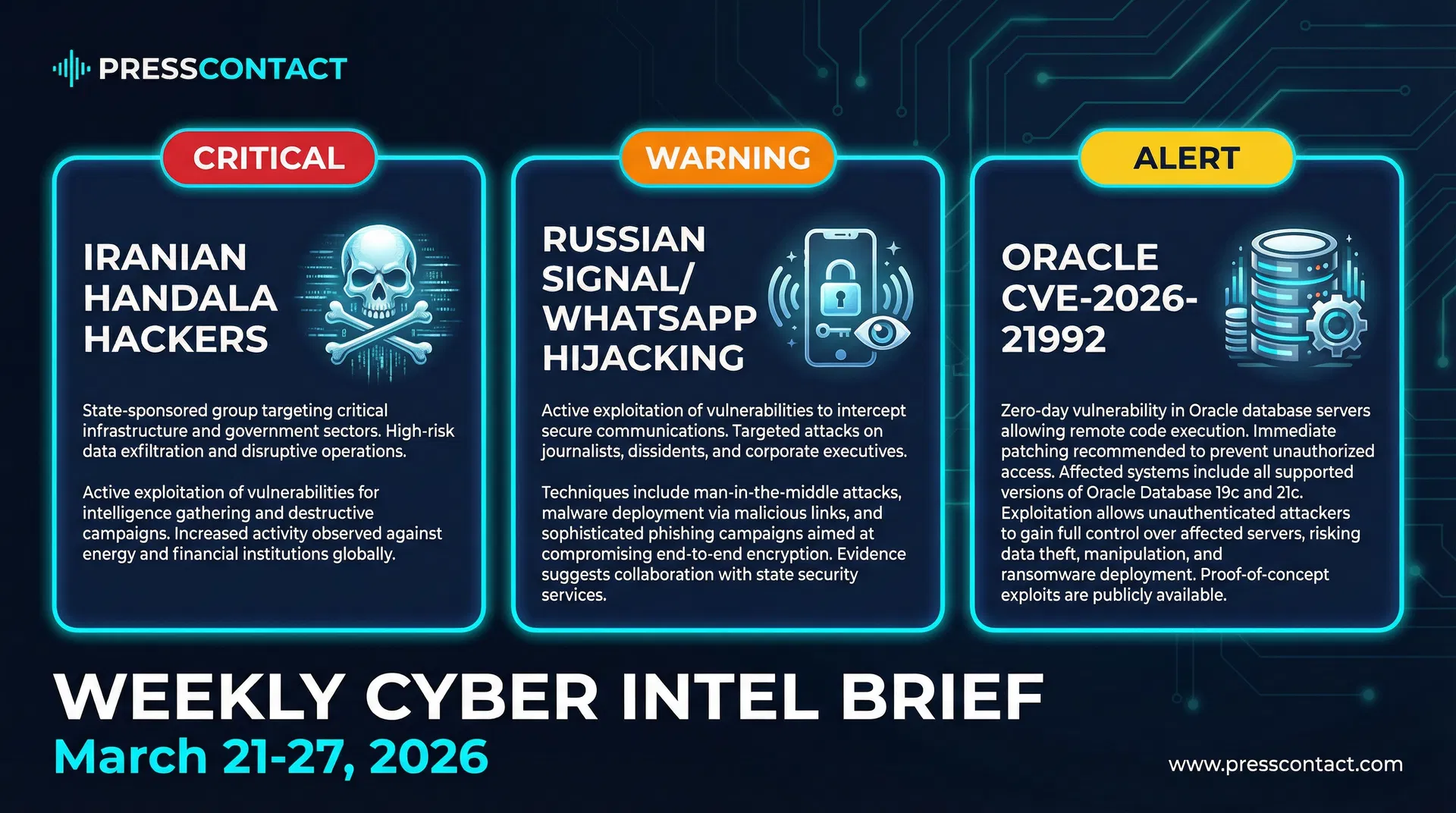
Weekly Cyber Intel Brief - Week of March 21-27, 2026
Iranian hackers conduct destructive attacks on U.S. infrastructure, Russian threat actors hijack Signal and WhatsApp accounts at scale, and Oracle releases critical RCE patch as attackers target vulnerable systems.
PressContact tracks the cybersecurity stories generating the most media coverage and security team attention each week. Here are the three that defined the week of March 21-27, 2026.
1. Iranian Cyber Operations Target U.S. Infrastructure - Handala Group Claims Responsibility
The Iranian-linked Handala hacker group conducted a series of destructive cyberattacks against U.S. infrastructure this week, claiming responsibility for multiple intrusions and data exfiltration operations. The group used the Handala-hack[.]to domain to publish stolen data and communicate attack claims, with Unit 42 researchers documenting the group's use of phishing, hacktivist activity, and coordinated cybercrime tactics.
The attacks generated significant social media traction, trending on TikTok and Facebook as users compared real-world events to fictional depictions of cyberattacks in popular media. The Handala group's public messaging and data publication strategy represents a shift toward psychological operations - using media attention and public disclosure as part of the attack strategy itself. This is not just about stealing data; it's about amplifying the impact through public awareness and fear.
For communications professionals, this incident highlights the need for rapid incident response messaging. Organizations targeted by state-sponsored actors need to coordinate with federal agencies (FBI, CISA, NSA) and prepare public statements that acknowledge the threat without overstating impact or revealing operational details. The Handala group's social media strategy means that public disclosure will happen - the question is whether your organization controls the narrative or lets adversaries define it.
2. FBI and CISA Warn of Russian Hackers Hijacking Signal and WhatsApp Accounts at Scale
The FBI and CISA, working with European law enforcement agencies, issued a joint warning about a widespread social engineering campaign targeting Signal and WhatsApp users. Russian-linked threat actors are using phishing, SIM swapping, and account takeover techniques to compromise encrypted messaging accounts at scale, gaining access to sensitive communications of government officials, corporate executives, and journalists.
The campaign is notable for its simplicity and effectiveness. Rather than targeting encrypted messaging protocols directly (which would require significant technical sophistication), attackers are targeting the authentication mechanisms - phone numbers, recovery codes, and backup authentication methods. Once they control the account, they have full access to message history, contacts, and ongoing communications. The attack is easily scalable because it relies on social engineering rather than zero-day exploits.
The communications angle here is critical: organizations that rely on encrypted messaging for sensitive communications (M&A discussions, crisis management, legal strategy) need to implement additional authentication layers and communication protocols. This is not just a personal security issue - it's an enterprise risk. Companies should update their incident response plans to account for the possibility that encrypted channels may have been compromised, and prepare alternative communication strategies for sensitive discussions.
3. Oracle Releases Critical Security Patch for CVE-2026-21992 - Remote Code Execution Vulnerability
Oracle released an emergency security patch for CVE-2026-21992, a critical remote code execution vulnerability affecting multiple Oracle products. The vulnerability allows unauthenticated attackers to execute arbitrary code on affected systems, and Oracle's advisory indicates that the flaw is being actively exploited in the wild. The patch was released with minimal advance notice, suggesting Oracle was responding to active exploitation.
The vulnerability is trending on security social media (X, Reddit, LinkedIn) because of its severity and the speed of exploitation. Security teams are racing to identify affected systems and apply patches before attackers can establish persistent access. The attack surface is broad - any organization running vulnerable Oracle software is at risk, and the lack of authentication requirements means attackers don't need valid credentials to exploit the flaw.
For communications teams, this is a reminder that vulnerability disclosures and patch releases can create immediate business impact. If your organization uses Oracle products, you need to communicate patch status to leadership, customers, and partners quickly. Delay in patching creates liability - if your organization is breached through an unpatched CVE-2026-21992 vulnerability after Oracle released a patch, that's a negligence issue that regulators and plaintiffs' attorneys will scrutinize. Prepare proactive communications that demonstrate your organization's rapid response to critical vulnerabilities.
PressContact publishes the Weekly Cyber Intel Brief to help security vendors, PR teams, and communications professionals stay current on the stories generating the most coverage and industry attention. If you work in cybersecurity PR and want to discuss any of these stories, reach out directly.